You have client or customer data in your possession. It is part of running your business in a digital marketplace. If that data is breached, it could permanently damage your reputation. We talked in an earlier blog about types of malware. There are many steps that you can take to protect your systems and data. Here are a few suggestions to protect your business from malware.
Data Net Blog
Data Net Blog
So what happens when you get software that has been mixed with a strong dose of malicious intent? You get malware, the term used to describe all manner of software invasion that has been designed to do bad things to your computers, networks and digital devices. It may have been created to steal something from you, such as data that can be monetized. It may try to directly steal money from you by draining bank accounts, or using credit card numbers. Sometimes, malware’s intention may be political: it may be about governmental intrigue or industrial espionage, Or it may just be about showing off or causing chaos for its own sake. Whatever the motivation, every organization needs to be constantly on guard to protect its data. Failure to protect the data of your clients and employees can result in serious damage to your reputation and brand as well as lead to fines from regulatory bodies. It can also open you up to liability from individuals or groups that have been harmed.
Losing your phone can be a distressing experience. Not only does it leave you disconnected from the digital world for the time being, but it also poses significant security risks for you and your organization if you use it for work. Taking a few steps can help you reduce the damage and even help you retrieve your lost device. Here's what to do after you've lost your phone.
Digital waste encompasses all the unnecessary data cluttering our storage systems until we decide to address it. This includes redundant files, outdated emails and chats, and forgotten photos gathering digital dust. While dismissing digital waste as a mere inconvenience is tempting, its implications are unfortunately significant.
Personally identifiable information—or PII—is critically important data for individuals and businesses, not only because operations rely on many of these data points but there are also significant circumstances for losing it. Of course, to properly protect PII, you need to know what the umbrella term of PII includes.
We all know that basic hygiene is a must to lead a healthy life. Did you know that the same rule applies to IT as well? There’s something known as cyber hygiene that plays a key role in keeping your business healthy from the IT perspective. So, how do you ensure your business doesn’t fail when it comes to cyber hygiene? Here are a few tips.
The idea of a four-day workweek—where the common 40-hour week is shortened to 32 with no reduction of benefits or take-home pay—is becoming increasingly popular, boasting improved efficiency and heightened levels of employee satisfaction.
Naturally, as an IT provider, we’re intrigued by the idea of using technology to get the most out of this abbreviated time in the office.
Who doesn’t like online shopping? Online shopping has opened up a whole new world to us. Get whatever you want, whenever you want, without wandering from store to store. It doesn’t matter if it is too hot to venture outside or if there’s a blizzard out there, you do your shopping from the comfort of your couch and the stuff at your doorstep. You get great deals, some are better than in-store specials. But, did you know cybercriminals love the concept of online shopping as much as you do. Cybercriminals are exploiting the growing popularity of online shopping to cheat unsuspecting buyers through techniques such as phishing, malware injection, etc. Here are a few tips that may work to keep you safe from being a target of cybercriminals as you shop online.
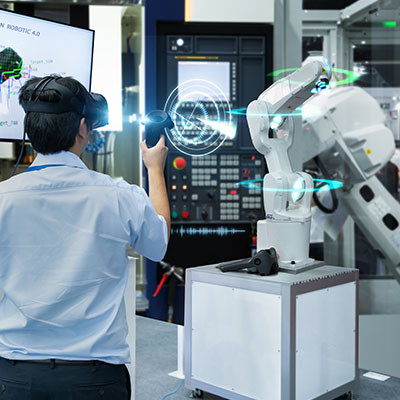
Technology is usually at the forefront of any major shift in a business’ operations to at least some degree. One interesting technology that has emerged in certain workplaces is augmented reality, or AR for short. Today, we’re considering specific instances where a business can implement AR to surprising benefits.
When we call ourselves a managed service provider (MSP), it still isn’t common knowledge what we mean by that. Perhaps the simplest way to describe our role is to call us an outsourced IT support provider, but even this definition falls short of the value we can offer. To remedy this, we wanted to review what one of our clients expects (and rightly so) to receive from a partnership with us.
Prioritizing cybersecurity is mandatory for all business owners, but many don’t know where to start. As a result, many businesses deal with cybersecurity issues that can put them behind and even ruin a good thing. In today’s blog, we provide a guide that explains the basics of cybersecurity for anyone to follow.
Artificial intelligence has become one of the most talked-about technologies throughout every sector of society. It’s being widely used in business, education, and civic life. We want to focus on the latter element and discuss how the U.S. Department of Homeland Security is using AI to improve its ability to keep Americans safe.
In one of the most common poisoning attacks, the attacker poisons the DNS Cache with the aim of leading visitors to a fake website. In a DNS cache poisoning case, the attacker gains control of the DNS server and then manipulates cache data such that anyone typing the URL of the actual website is redirected to the fake one. This could be a phishing site where the attacker would have carefully laid out a trap to capture the unsuspecting victim’s personal data or secure information. For example, the visitor thinks they are logging into their bank’s website online, but are actually on the attacker’s phishing site, where they enter the login credentials.
For any organization that depends on its wireless network, your router is a critical piece of hardware that does more than you may realize. From broadcasting wireless Internet signals to protecting your network from harm, knowing exactly what to do with your router is good knowledge to have. Today, we’ll go through some of the things you should know about your router that will allow you to improve your organization's Wi-Fi significantly.
Smart technology is everywhere. Not just in our offices, but even in our day-to-day lives with tools like Google Home and Alexa becoming a commonplace. With technology becoming smarter every minute, the risks are increasing by the minute as well. Cybercriminals are finding new ways to corrupt our IT networks to disrupt our businesses, hold our data hostage and even clear our personal bank accounts. Some of the more overt, commonly known acts of cybercrime include hacking, phishing, and ransomware attacks. This blog discusses a lesser-known cybercrime--Poison attacks.
The modern business landscape is fueled, in large part, by something we refer to as professional services. This typically includes any business model with trained professionals at the center of the business. In today’s economy, this can include tradesmen, but typically, it means consultants, lawyers, agents, and other professionals essential to moving business forward. Today, we thought we would briefly go into some of the technologies that professional services depend on.
When you run a business, it’s often hard to know what to do. There are several strategies that you could potentially implement for every single part of your business. When things go right, you look like a genius; when things go horribly wrong, you can look like a fool. In this blog, we plan on outlining some things that every business owner should do to improve their business.
There are plenty of reasons why you might have employees working while out and about on travel, whether it’s for conferences, professional development sessions, or otherwise. Traveling with technology can be stressful and dangerous, though, particularly if you aren’t taking preventative measures. Today, we want to discuss what you can do to keep your entire team’s technology safe while they are traveling.