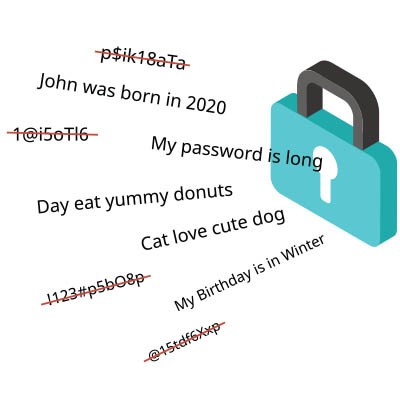
Cybersecurity tops the list for any business’ needs, particularly when one considers just how many threats are out there today. This makes it essential that today’s businesses (yours included) put an assortment of cybersecurity tools and protections in place.
We’ve assembled a list of the ones we recommend.