Welcome to the human side of cybersecurity! Today, we're not talking about fancy algorithms or high-tech firewalls. Instead, we're focusing on the most crucial element in your cybersecurity arsenal – your team. Just like a sports coach hones the skills of their athletes, it's vital to train your team in the art of cyber defense. So, let's dive into why employee training isn't just a nice-to-have, but a must-have in your cybersecurity playbook.
Data Net Blog
Data Net Blog
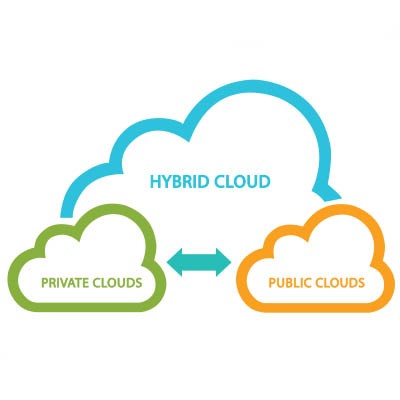
If you want to discuss the single most influential technology for the modern era, there’s a lot of competition—but the cloud is a serious contender. Through the cloud, your organization can pull off feats previously impossible for all but the largest and most profitable companies. Today, we want to look at how small businesses use the cloud and how you benefit from the various models.
Today, we're rolling up our sleeves and diving into the world of cyber hygiene. Just like you wouldn't leave your house without brushing your teeth (hopefully!), you shouldn't navigate the digital world without basic cybersecurity practices. In our series, we’ve been focused on small and medium-sized businesses, especially those in the construction industry, but this applies to just about every organization. It's all about keeping your digital environment as sparkling clean as your kitchen counter. So, let's get into the nitty-gritty of cyber hygiene and why it's as essential as your morning shower.
It is a known fact that survival of any species depends on its ability to adapt to change. One major change for businesses in 2020 was the need to switch to the work-from-home model to keep things running during the time of pandemic. When countries all over the world started imposing lockdown restrictions, companies had no choice but to switch to remote operations if their line of business allowed them to do so. This blog post discusses the key challenges faced by businesses that had failed to adopt the latest technology on time.
Hello, DoD contractors and cybersecurity enthusiasts! Today, we're diving into the world of CMMC 2.0, the updated version of the Cybersecurity Maturity Model Certification. Gone are the days of five levels of complexity; CMMC 2.0 simplifies things down to three levels. It's like going from a confusing remote with too many buttons to a sleek, three-button interface. Let's break down these levels in a way that's as straightforward as your favorite morning routine.
Business is built on relationships, and to be frank, some can be quite challenging. Think about all the difficulties you’ve faced with customers, vendors, or employees. Sometimes, it's hard to imagine how your business could succeed without these key players, but they all can be a drain on any given day. Today, we’ll explore how the relationships you build in business can be the deciding factor in your success.
The COVID-19 pandemic has changed life as we know it, in many ways. While its impact on our day-to-day lives has been huge, the impact has been even more severe from a business perspective. The social distancing norms, staggered operating hours so as to limit crowds, the masks, shields, barriers, and what-not! From the business continuity perspective, companies have had to adapt themselves to the new normal very quickly.
Today, we're diving into the toolbox of cybersecurity – a place where digital hammers meet virtual nails. If you're a DoD contractor, especially in the construction sector, this is where you'll find the essential tools and practices to not only comply with regulations but also to fortify your digital fortress. So, grab your digital tool belt, and let's explore the tools that will keep your business safe and compliant.
The United Nations is responsible for protecting human rights all over the world, as well as creating more sustainable and climate-friendly policies. With the rise of artificial intelligence being at the forefront of many countries’ technological innovations, it’s natural that AI would be thrust into the crosshairs at some point. The UN hopes to develop guidelines that protect people’s access to and use of AI without allowing it to cause more significant problems.
Welcome to the world of cybersecurity, where the only constant is change, and the only sure defense is staying informed and prepared. If you're a Small and Medium-sized Business (SMB) in the construction sector working with the Department of Defense (DoD), you've probably heard about the Cybersecurity Maturity Model Certification (CMMC). But what is it exactly, and why is it as important as that morning cup of coffee for your business? Let's break it down in a way that won't require a cybersecurity dictionary.
Running a small business often inspires dreams of rapid expansion and immediate success. However, it’s crucial to balance ambition with realistic expectations to ensure sustainable growth. In today’s blog, we’ll discuss how entrepreneurs and managers can set achievable goals while maintaining business stability.
Sextortion scams are far from glamorous. These attacks involve a scammer claiming to have compromising photos or videos of their target engaged in explicit activities—often suggesting this footage was captured through their online behavior. The scammer then threatens to release this material unless a ransom is paid.
Managed IT services are becoming more popular by the day. Businesses, big and small, are bringing managed service providers onboard to handle their IT requirements. The bigger IT players like IBM, Accenture, CISCO act as MSPs to larger organizations, while the typical managed service provider is often hired by SMBs. However, there’s a question that crops up time and again--Do SMBs really need an MSP? SMBs are sometimes in two minds when it comes to bringing an MSP on board and typically use one of the following justifications.
Our IT requirements are limited
A lot of businesses in the small to mid-size range believe that their IT needs don’t warrant a full-time service level agreement with an MSP. They believe the only times they need to invest in IT is at the start of their business or when rolling out new technology. As a result, they don’t see much value in signing a service level agreement with an MSP.
We are tight on budget
SMBs also tend to cut on the IT budget and invest those funds elsewhere--generally in areas where they see tangible results, such as hiring new customer-facing staff or a new advertising campaign. So, when SMBs find themselves a little tight on the budget, the IT department sees the cut.
We have our in-house IT person/team
Businesses with an in-house IT expert or even a small in-house IT team feel that is sufficient for handling any IT needs and an SLA is just an added expenditure.
So, did your reason make it to the list? Stay tuned for our next blog post, where we will discuss how an SLA with a managed service provider can add value to your business.
Communications are huge for a business, and in the course of doing business, no other communication tool is as valuable as the telephone. Today’s businesses have a real choice on how they want to purchase their telephone system, and the more your business relies on collaboration and innovative communications tools such as video conferencing, the more it becomes evident that VoIP is the best option. Today, we’ll explain how VoIP can bring substantial value to your business.
In a recent industry survey, it was found that one of the biggest factors holding back small and mid-sized firms from achieving their business goals was IT. One may argue that smaller businesses lack the capital that the bigger players have to invest in their business, but even with all other aspects being more or less equal, the difference brought about by their lack of investment in IT was found to be a key differentiating factor--far more than other elements such as marketing, human resources and even industry expertise.
AI is everywhere and it could be said that it is transforming the modern economy. With each passing day the technology is becoming an essential tool for businesses looking to boost their overall business efficiency. Small businesses can use AI in a number of ways and in today’s blog, we’ll explore how they can use AI to their advantage.
Many small or mid-sized businesses don’t focus much on IT as they should. For a lot of them, the focus is on customers, ensuring they have enough staff to meet their client needs, expanding their business and driving revenue by selling. IT comes into the picture initially when the business is being set up. Once they have their IT infrastructure up and running, it tends to take a backseat. The typical mid-sized or small business owner seems to prefer the firefighting approach to IT--meaning, they reach out to an IT service provider only when they have an IT problem.